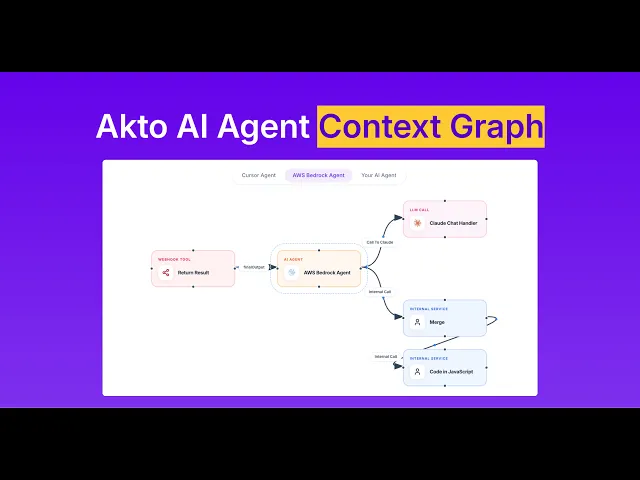
Map Your AI Agents with Akto Agent Context Graph
Akto Agent Context Graph auto-discovers and maps every connection in your agentic system - agents, MCP servers, LLMs, databases, and external APIs.

Krishanu
Your AI agents don't operate in isolation. They call MCP servers. MCP servers hit external APIs. External APIs access databases. One compromised connection, and the blast radius can span your entire agentic architecture.
The problem?
Most security teams have zero context into how these components are connected. They're securing individual agents and endpoints without understanding the web of dependencies between them.
That's the gap Akto's AI Agent Context Graph closes.
The Visibility Problem in Agentic AI
Traditional Security tools were built for a simpler world, one where you had a known set of endpoints, predictable request-response patterns, and clear boundaries between services.
Agentic AI blows that model apart. A single AI agent might orchestrate calls across multiple MCP servers, each of which connects to different external tools and data sources. An agent built on LangChain might call a Slack MCP server, which queries an internal database, which triggers a webhook to a third-party analytics service. The chain of dependencies is deep, dynamic, and, in most organizations, completely undocumented.
Without a map of these connections, security teams are left guessing:
Which agents have access to sensitive data?
What happens if an MCP server is compromised - what else is exposed?
Are there circular dependencies that could be exploited?
Which external services represent the highest risk?
You can't secure what you can't see.
What Is the AI Agent Context Graph?
The AI Agent Context Graph is a visual, interactive map of your entire agentic architecture. It auto-discovers and renders the relationships between every component in your system: AI agents, MCP servers, external tools, databases, and third-party services.
Think of it as a dependency graph - but purpose-built for agentic AI security.
Instead of manually documenting how Agent A connects to MCP Server B, which calls External Service C, the Context Graph does it automatically. It ingests traffic data from Akto's connectors across 50+ agent builder platforms (AWS Bedrock, Google Vertex, Azure AI, LangChain, CrewAI, and more), and builds a real-time topology of every connection.
The result: one graph, every connection.
Akto Agent Context Graph is now live on Product Hunt - support us with an upvote!
How It Works
The workflow is straightforward:
1. Connect Akto to your Agent Builder Platforms.
Akto supports native connectors for AWS Bedrock, Google Vertex, Azure AI Foundry, and 20+ other platforms. Plug in your infrastructure, and Akto starts ingesting traffic.
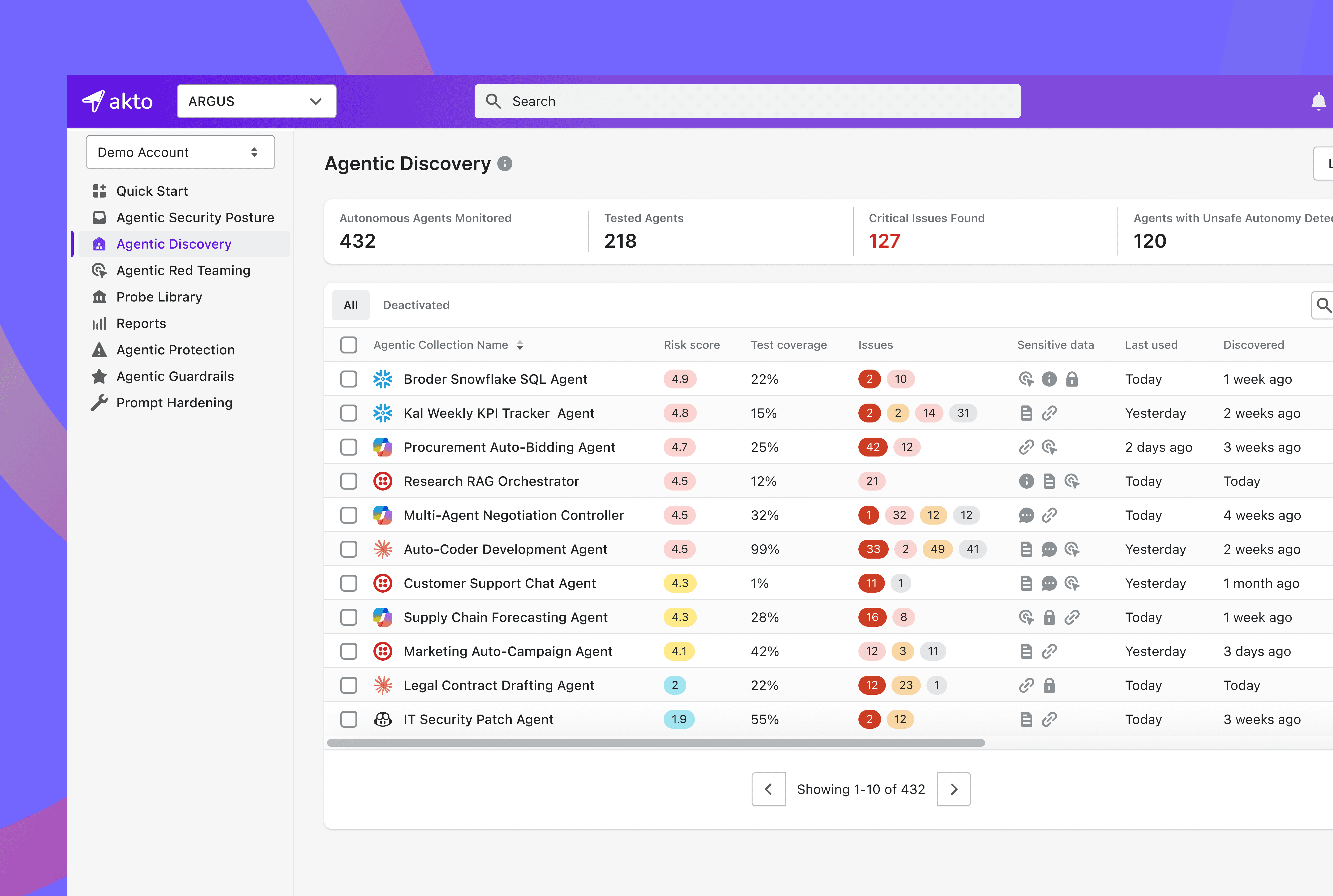
2. Akto Creates an Inventory of all Agents.
Every AI agent running across your cloud, on-prem, or hybrid environment gets cataloged automatically, including shadow agents and zombie agents you didn't know existed.
3. The Context Graph renders the Full Topology.
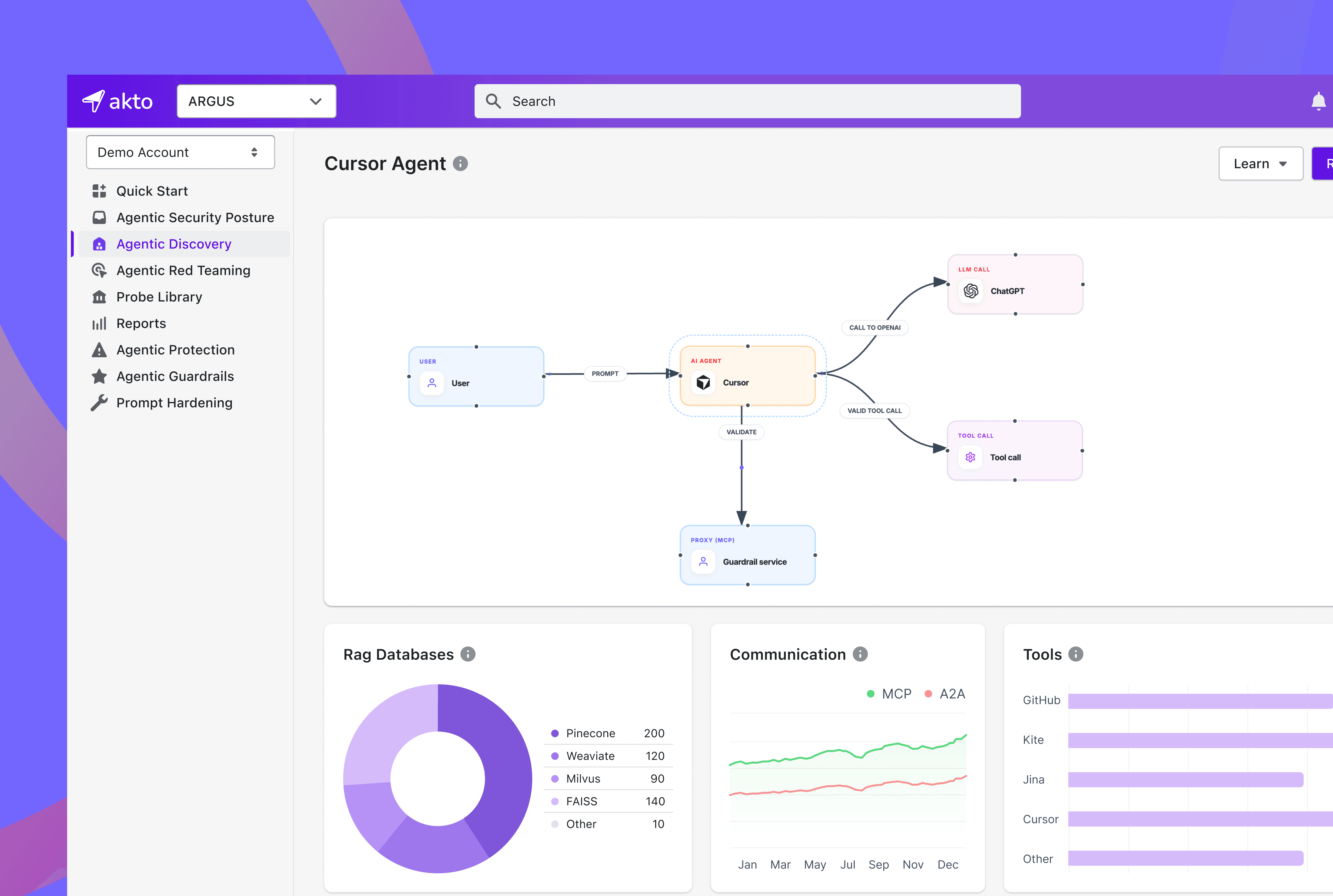
Navigate to Agentic Discovery, select an agent collection, and open the Context Graph tab. You'll see a visual map showing every agent, every MCP server, every external service, what tools they are calling and how they're all connected.
Why This Matters for Security Teams
The Context Graph isn't a nice-to-have visualization tool. It's the foundation for several critical security workflows.
Impact Analysis
When you need to patch an MCP server or rotate credentials for an external API, the Context Graph shows you exactly which agents and services will be affected. No more guessing. No more surprise outages.
Attack Path Identification
A compromised tool node that connects to an MCP server with access to sensitive databases is a different risk than a standalone tool. The Context Graph makes these attack paths visible so you can prioritize hardening where it matters most.
Architecture Review
As your agentic infrastructure scales, the Context Graph gives engineering and security teams a shared, up-to-date view of how the system is actually wired - not how someone documented it six months ago.
Compliance Documentation
Regulations increasingly demand documentation of data flows, especially where AI is involved. The Context Graph provides an auditable, real-time map of where data goes, which components touch it, and how it moves through your system.
Red Teaming Prioritization
The Context Graph directly informs where to focus your AI red teaming efforts. High-connectivity nodes with access to sensitive data are your highest-priority targets.
Best Practices
If you're deploying the Context Graph, here's how to get the most out of it:
Review it regularly. Agentic architectures evolve fast. What was a three-node system last month might be a fifteen-node web this month.
Watch for circular dependencies. They're common in complex agentic setups and can be exploited to create infinite loops or amplify attacks.
Monitor third-party dependencies. Every external service is a node you don't fully control. Track them, assess their risk, and have a plan for when one goes down.
Use it to plan red teaming. Don't red team randomly. Let the graph tell you where the critical paths are.
Tie it to incident response. When something goes wrong, the Context Graph is your first stop for understanding blast radius.
The Bigger Picture
The AI Agent Context Graph is part of Akto's broader approach to agentic AI security. It works alongside Akto's agent inventory, risk scoring, sensitive data detection, shadow agent discovery, and agentic red teaming capabilities to give security teams end-to-end visibility and control over their AI infrastructure.
Because in a world where agents call agents, which call MCP servers, which call APIs, which access databases, the organization that can see the full picture is the one that can actually secure it.
Ready to map your agentic architecture? Book a demo to see the AI Agent Context Graph in action.
Experience enterprise-grade Agentic Security solution

