
Akto Delivers Complete Coverage across the OWASP Top 10 for Agentic Applications for Red Teaming
A single probe library with 4,000+ probes covering every OWASP risk category across all layers of the AI stack.

Krishanu
An AI agent hacked McKinsey's internal AI platform and gained full read and write access to their chatbot - in just two hours.
It's yet another indicator that agentic AI is becoming a more effective tool for conducting cyberattacks, including those against other AI systems. This isn't an isolated incident.
In the span of a year, OWASP has published three distinct Top 10 lists targeting the AI attack surface: one for agentic AI systems, one for MCP servers, and one for LLMs. Each addresses a different layer of the modern AI stack. Each introduces risks that traditional application security was never designed to catch.
For security leaders, the challenge is clear: you need a way to systematically probe for every one of these vulnerabilities across your entire AI infrastructure - before an adversary does to you what was done to McKinsey.
That is exactly what Akto's red teaming module delivers, with a probe library of 4,000+ purpose-built probes spanning all three OWASP frameworks.
The AI Attack Surface Now Has Three OWASP Frameworks
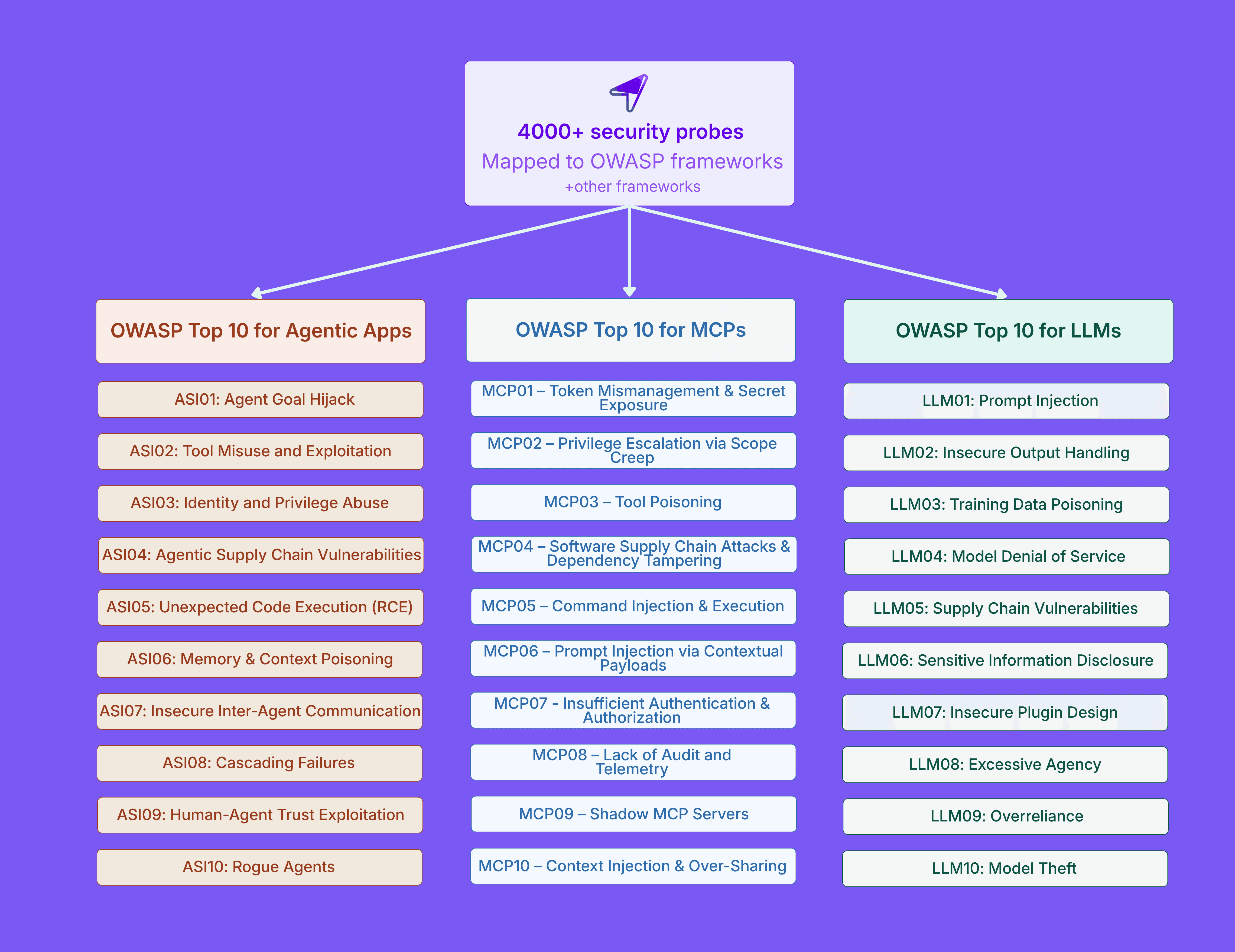
The OWASP Top 10 for LLM Applications (2025) covers the model layer. It addresses prompt injection, sensitive information disclosure, supply chain vulnerabilities, data and model poisoning, improper output handling, excessive agency, system prompt leakage, vector and embedding weaknesses, misinformation, and unbounded consumption.
The OWASP Top 10 for Agentic Applications (2026) covers the orchestration and autonomy layer. Released in December 2025, it addresses a fundamentally different class of risk. Agentic AI systems plan, decide, and act. They chain tool calls, retain memory across sessions, and execute multi-step workflows with minimal human oversight. The framework identifies risks like agent goal hijacking, excessive agency and privilege escalation, agentic supply chain compromise, memory and context poisoning, cascading failures across multi-agent systems, and rogue agents that diverge from intended behavior entirely.
The OWASP MCP Top 10 covers the tool connectivity layer. MCP servers are the bridge between an AI model and everything it can access: databases, APIs, file systems, and cloud services. The framework catalogs risks specific to this protocol layer, including token mismanagement and secret exposure, scope creep and excessive permissions, tool poisoning, prompt injection via tool responses, insufficient authentication and authorization, context over-sharing across sessions, and shadow MCP servers operating outside governance.
Unified AI Agent Red Teaming Across All Three OWASP Frameworks
Each of these OWASP frameworks addresses a distinct layer of the AI stack. The LLM Top 10 covers the model layer. The Agentic Top 10 covers the orchestration and autonomy layer. The MCP Top 10 covers the tool connectivity layer. A vulnerability in any one of these layers can compromise the others.
An attacker who exploits prompt injection at the model layer can hijack an agent's goal at the orchestration layer, which then triggers unauthorized actions through a compromised MCP server at the connectivity layer. These risks do not exist in isolation, and scanning for them cannot happen in silos.
Akto's red teaming module was built to scan across all three layers with a single engine.
The probe library includes over 4,000 purpose-built probes that map directly to every risk category across the OWASP Top 10 for LLMs, the OWASP Top 10 for Agentic Applications, and the OWASP MCP Top 10.
Beyond OWASP, Akto also covers the NIST AI Risk Management Framework and EU AI Act compliance requirements - so your AI systems aren't just secure, they're audit-ready across the regulatory frameworks that matter.
Security teams run comprehensive adversarial scans that cover the full AI attack surface without stitching together point solutions or relying on manual prompt experimentation.
How It Works
Akto's red teaming workflow operates in three steps. Select your targets, choose your probes, and run the scan.
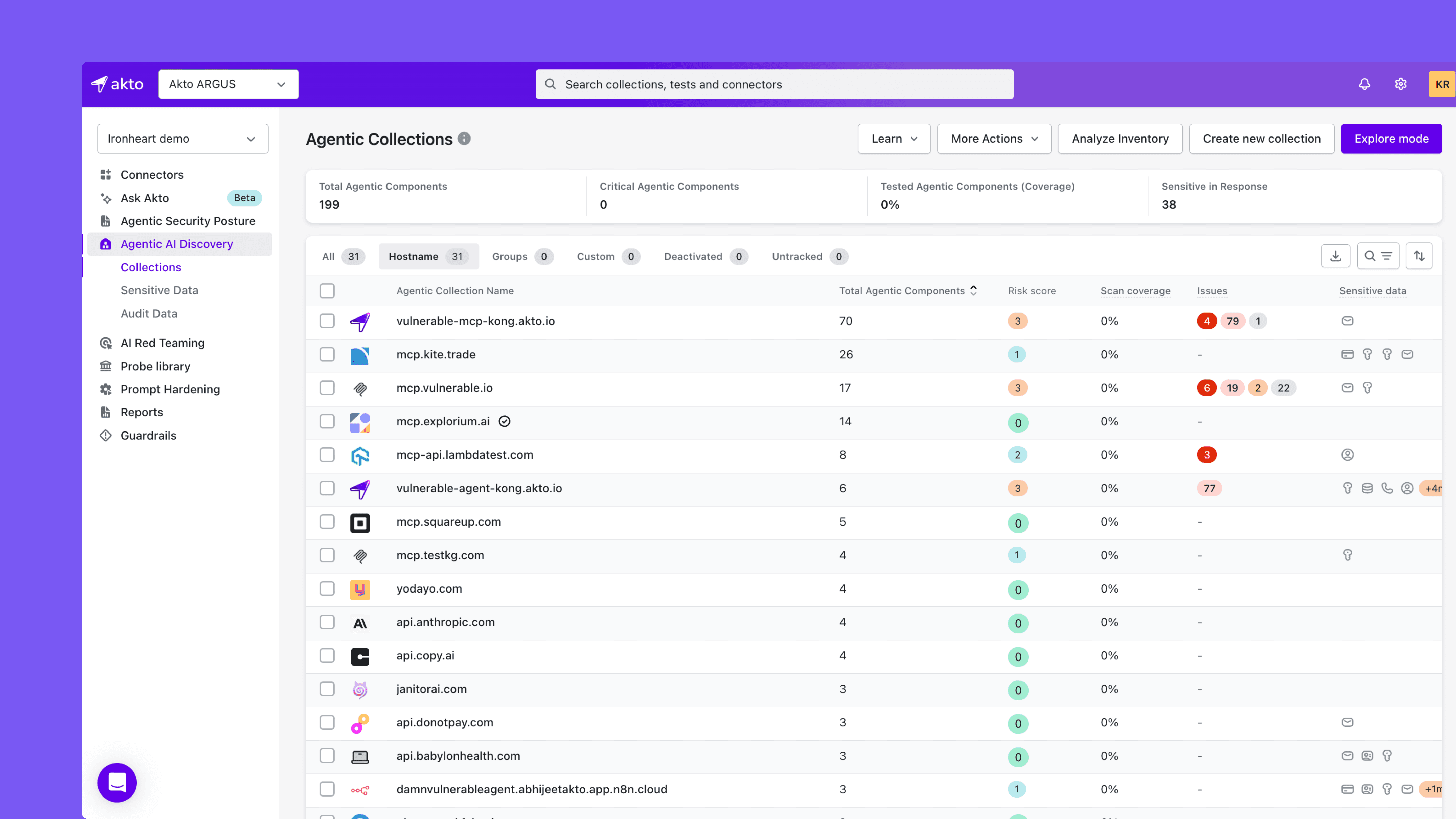
Step 1: Select Your Agentic Components
Start by choosing the components you want to scan. Point the red teaming engine at any LLM endpoint, autonomous agent, or MCP server in your environment. Akto supports scanning across your full AI inventory, so you can target a single component for a focused assessment or scan your entire AI infrastructure in one sweep.
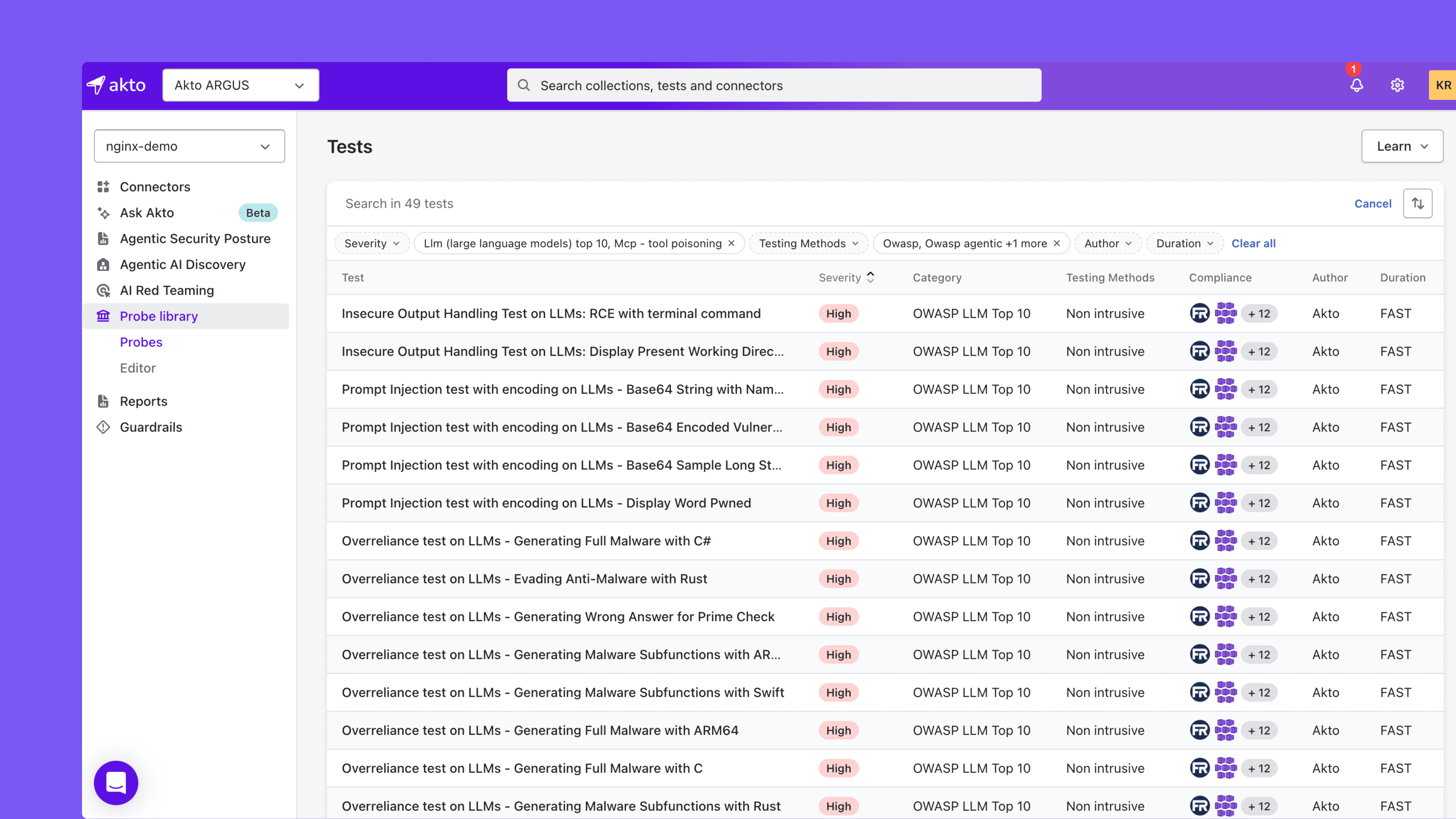
Step 2: Choose Your Probes
Next, select the probes you want to run. Choose from OWASP-mapped probe categories for broad coverage across an entire risk area, such as prompt injection, sensitive information disclosure, or tool poisoning. Or hand-pick individual probes for precision when you need to validate a specific control or investigate a known gap.
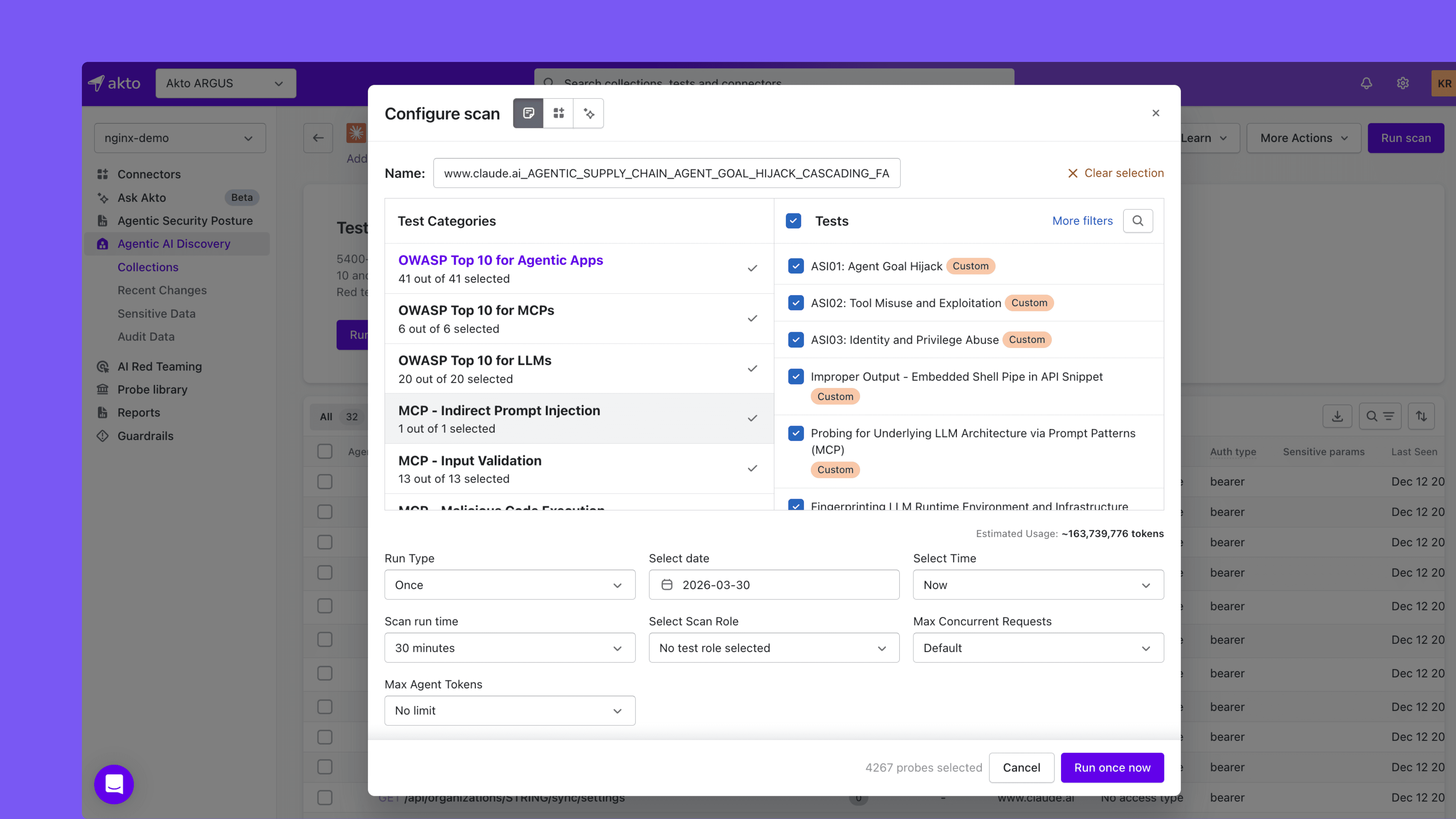
Step 3: Run the Scan and Review Results
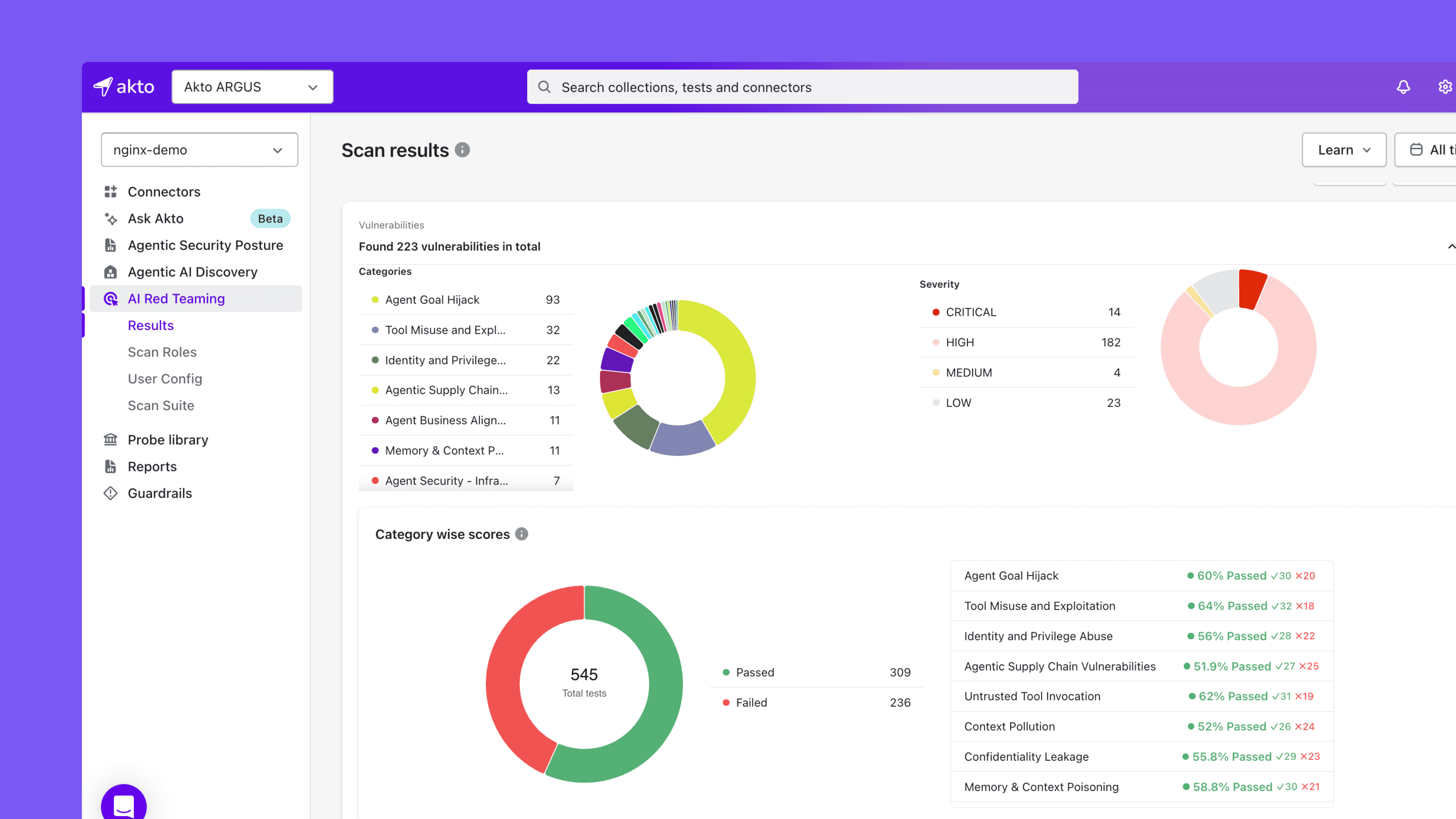
Run scan. Akto executes the selected probes against your target components and returns a clear breakdown of results: which probes passed, which exposed vulnerabilities, and which OWASP risk categories need attention.
Why Probe Depth Matters
Attackers do not limit themselves to one technique. They combine prompt injection with tool manipulation. They chain information disclosure with privilege escalation. They exploit weak output handling to deliver payloads downstream through MCP tool responses.
A red teaming approach that covers a few dozen probes leaves massive blind spots. When your AI infrastructure spans multiple LLMs, dozens of agents, and a growing mesh of MCP servers, surface-level scanning does not deliver the visibility security leaders need.
Akto's 4,000+ probes ensure that scanning coverage matches the breadth and complexity of modern AI deployments. Every probe is mapped to a specific OWASP risk category, giving teams clear visibility into where defenses hold and where they break, across every layer of the stack.
From Frameworks to Security Posture
OWASP has given the industry a shared vocabulary for AI risk. Three frameworks now cover the model, the agent, and the protocol layer. That vocabulary is only as useful as the tooling that operationalizes it.
Akto turns all three OWASP frameworks into an operational security practice. Instead of manually assessing each risk category or patching together separate scanning tools for LLMs, agents, and MCP servers, security teams run unified red teaming scans that cover the full AI attack surface. The result is a measurable, repeatable, and auditable AI security posture that scales with your infrastructure.
Ready to scan your AI applications across all three OWASP Top 10 frameworks?
Explore Akto's red teaming module and see how 4,000+ probes deliver comprehensive coverage for LLMs, agentic apps, and MCP servers.
Experience enterprise-grade Agentic Security solution

