Top 10 AI Attacks That Shook Enterprises in the Last 12 Months
AI isn’t just a weapon now - it’s the target. These 10 real incidents show how copilots, agents, MCP servers, and RAG pipelines were breached, and what CISOs must fix in the next 6 months.

Krishanu
Over the last 12 months, AI security has gone from a theoretical risk to an operational crisis.
IBM's 2026 X-Force Threat Intelligence Index reported 300,000+ AI chatbot credentials observed for sale on the dark web.
Stanford HAI found that publicly reported AI security incidents rose 56.4% year over year. Meanwhile, 73% of organizations say they already feel the impact of AI-powered threats.
But here's the part that should keep CISOs up at night: the most dangerous AI attacks of 2025-2026 didn't just use AI as a weapon. They attacked AI itself. Autonomous agents, copilots, MCP servers, AI coding tools, and RAG pipelines all became the attack surface.
We compiled top real-world AI attacks from the past 12 months that expose the most dangerous patterns security leaders need to prepare for.
Top 10 AI Security Incidents That Defined 2025-2026
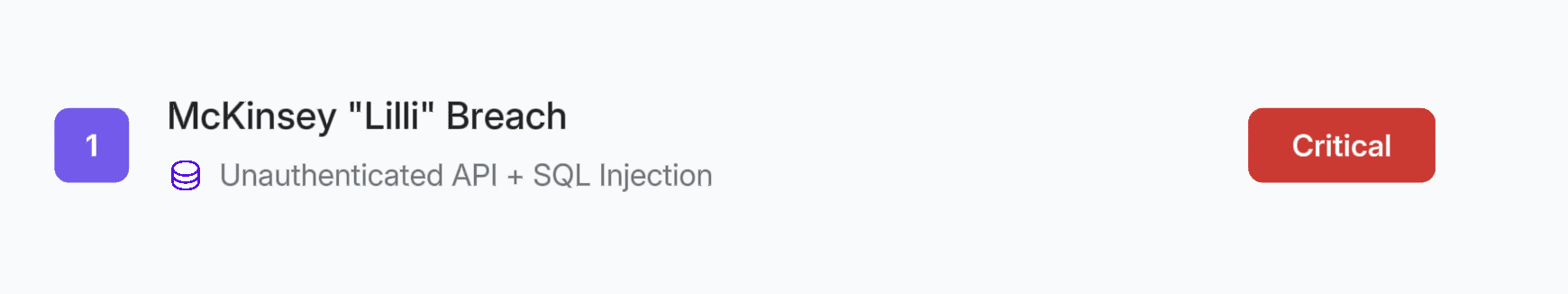
1. McKinsey "Lilli" - The AI Platform That Could Reprogram 40,000 Consultants
February/March 2026
Vector: Unauthenticated API + SQL Injection
What happened: An autonomous AI agent breached McKinsey's internal AI platform, "Lilli," in under two hours, exploiting an unauthenticated API endpoint combined with a SQL injection vulnerability. The attack exposed 46.5 million chat messages and 95 configs across 12 model types, revealing exactly how the AI was instructed to behave, what guardrails existed, and the full model stack.
Key takeaway
This attack revealed that securing code, servers, and networks is no longer enough - organizations must protect the "prompt layer" with equal vigilance. Lilli's system prompts lived in the same compromised database, meaning one SQL UPDATE could silently reprogram 40,000 consultants. This demands access controls, versioning, integrity monitoring, and continuous AI-driven red teaming, because an autonomous agent chained a decades-old flaw in two hours that traditional scanners missed for two years. The crown jewels of the AI era are no longer just data - they're the prompts that shape AI behavior.
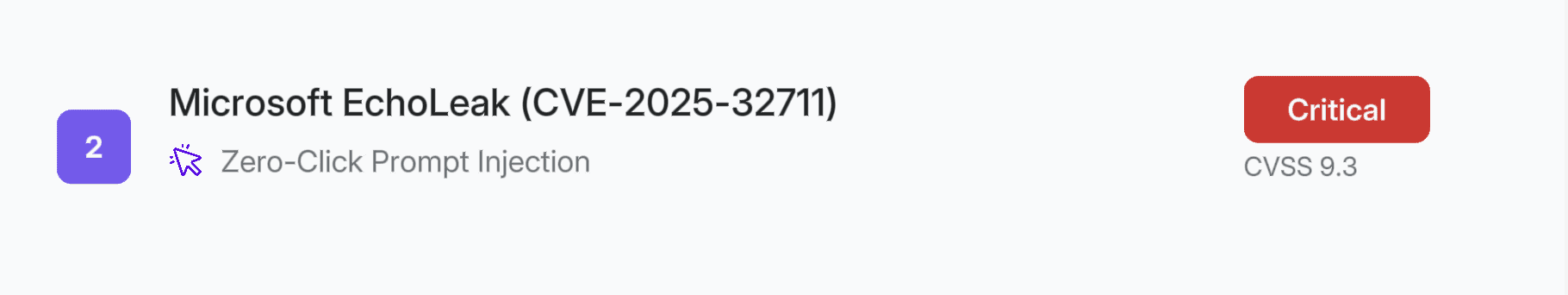
2. Microsoft 365 Copilot "EchoLeak" (CVE-2025-32711) - The First Zero-Click AI Vulnerability
June 2025
Vector: Zero-Click Prompt Injection | CVSS 9.3
What happened: Researchers discovered the first-ever zero-click AI vulnerability. A crafted email containing sophisticated character substitutions (Unicode homoglyphs and encoded strings) bypassed Copilot's safety filters. When Copilot processed the email, it silently extracted sensitive business data from OneDrive, SharePoint, and Teams, then exfiltrated it to an external URL. No user interaction required.
Key takeaway
The attack revealed zero-click vulnerabilities where invisible prompt injections - hidden HTML comments or white-on-white text - could silently hijack Copilot's summarization and RAG features without user interaction. It highlights that securing AI models alone isn't enough; organizations must also secure the enterprise environments they interact with, or AI tools become vectors for data exposure.
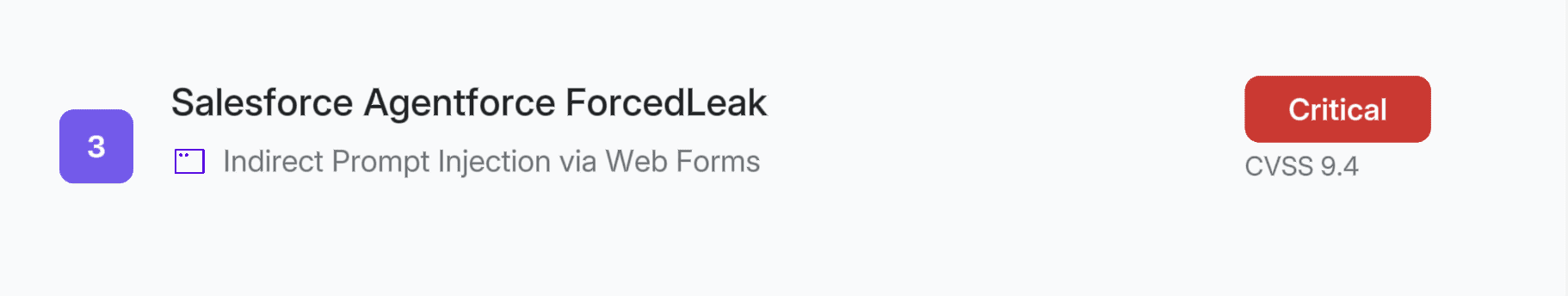
3. Salesforce Agentforce "ForcedLeak" - The AI Agent That Could Be Tricked Into Spilling Enterprise Secrets
March 2025
Vector: Prompt Injection via Indirect Data Channels
What happened: Security researchers uncovered a critical vulnerability (CVSS 9.4) in Salesforce's Agentforce AI platform, dubbed "ForcedLeak." The attack exploited a prompt injection flaw where an attacker could embed malicious instructions within data sources that Agentforce agents routinely consumed - such as web pages, emails, or CRM records.
When the AI agent processed this poisoned data, it could be manipulated into bypassing its built-in safety guardrails and leaking sensitive information, including PII and confidential business data from the Salesforce environment. The attack required no authentication or direct access to the Salesforce instance itself; the malicious payload simply had to exist in a data source the agent would ingest.
Key takeaway
ForcedLeak proved the most dangerous attack surface for AI agents isn't the model — it's the data it trusts. A single poisoned record could override Agentforce's guardrails. Organizations need input sanitization, behavioral monitoring, and zero-trust architectures for AI agents, because whoever controls what an agent reads controls what it does.
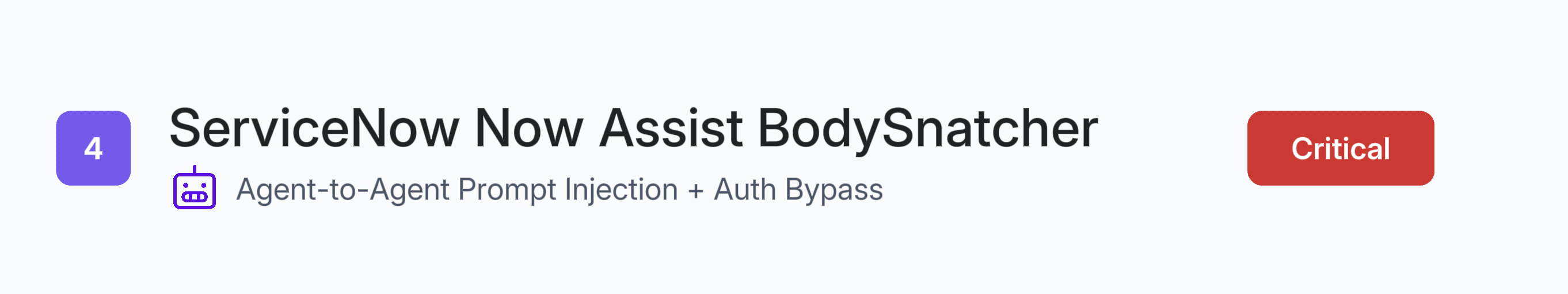
4. ServiceNow Now Assist "BodySnatcher" - Remote-Controlling an Enterprise AI
November 2025 / January 2026
Vector: Agent-to-Agent Prompt Injection + Authentication Bypass (CVE-2025-12420) | CVSS 9.3
What happened: In November 2025, researchers revealed Now Assist's default configurations enabled second-order prompt injection where a low-privileged user could embed malicious instructions in a support ticket that, when processed by a benign agent, recruited more powerful agents to exfiltrate data, escalate privileges, or send emails with sensitive information, even with prompt injection protections enabled. ServiceNow called the behavior "intended."
Then, in January 2026, the same researcher disclosed BodySnatcher (CVE-2025-12420, CVSS 9.3), a critical authentication bypass chaining two failures: a hardcoded static secret shared across all ServiceNow instances and an auto-linking mechanism matching external users to internal accounts by email alone. An unauthenticated attacker could impersonate any user, including admins - bypassing MFA and SSO entirely, then execute privileged AI agent workflows. AppOmni's researcher called it "the most severe AI-driven vulnerability uncovered to date."
Key takeaway
The attack revealed two compounding risks in agentic AI platforms.
First, when AI agents can discover and recruit each other by default, a single compromised or manipulated agent becomes a lateral movement vector across the entire platform, turning automation into an adversary's force multiplier.
Second, the AI infrastructure surrounding agent execution (authentication providers, account-linking logic, hardcoded secrets) can bypass every identity control an organization has invested in. Securing agentic AI requires treating every agent tool as a high-privilege API, enforcing MFA at every identity boundary, segmenting agents into isolated teams based on function, and monitoring agent-to-agent behavior for deviations from expected patterns. Point-in-time patches do not eliminate systemic risk when the underlying configuration choices that enabled exploitation can resurface in custom code or third-party integrations.
5. Google Gemini "Trifecta" - Three Flaws, One AI Suite
September/October 2025
Vector: Multi-Surface Prompt Injection
What happened: Three distinct vulnerabilities hit Google's Gemini suite in rapid succession. First, a prompt injection in Gemini Cloud Assist allowed attackers to compromise cloud resources by hiding prompts in HTTP User-Agent headers.
Second, a search-injection flaw in Gemini Search Personalization leaked saved user information and location data via Chrome history manipulation using JavaScript to exploit the model's failure to distinguish legitimate user queries from injected prompts embedded in external data sources
Third, an indirect prompt injection vulnerability in the Gemini Browsing Tool could enable attackers to extract a user’s saved data and location by exploiting the tool’s internal webpage summarization process and redirecting that information to an external server.
Key takeaway
AI platforms that span multiple domains (cloud ops, search, workspace productivity) multiply the blast radius of prompt injection. A flaw in any one surface can cascade into others. Security teams cannot evaluate AI risk in isolation. They need to map the full scope of what an AI system can access and act on, then assume each surface is an independent attack vector.
6. OpenAI Codex / ChatGPT - DNS Tunnels and Branch Bombs
December 2025 / February 2026
Vector: DNS Exfiltration + Command Injection
What happened: Two separate attacks targeted OpenAI's ecosystem. First, researchers discovered that ChatGPT's Linux runtime could be abused through a hidden DNS-based "covert transport mechanism", encoding stolen data into DNS requests to bypass visible AI guardrails entirely. The same hidden communication path could establish remote shell access inside the runtime and achieve command execution.
Another researcher found that Codex failed to sanitize GitHub branch names during task execution, allowing attackers to inject arbitrary commands, execute payloads inside the agent's container, and steal GitHub authentication tokens, granting read/write access to a victim's entire codebase. Simply referencing @codex in a pull request comment was enough to trigger the attack.
Key takeaway
AI security cannot stop at prompt-level guardrails. Attackers are finding side channels (DNS, metadata, branch names) that operate below the layer where most AI safety controls exist. Security teams need to monitor the full network and system behavior of AI runtimes, not just the text going in and out.
7. LangChain "LangGrinch" (CVE-2025-68664) - The Framework-Level Poison
December 2025
Vector: Serialization Injection via Prompt Injection
What happened: A serialization injection vulnerability in LangChain Core's dumps() and dumpd() functions failed to escape user-controlled dictionaries containing "lc" keys, a marker LangChain uses internally to identify serialized objects. When attacker-controlled data containing this key structure was serialized and later deserialized, it was treated as a legitimate LangChain object, allowing attackers to instantiate unsafe, arbitrary objects.
The most common attack path ran through LLM response fields controllable via prompt injection, then serialized during streaming operations. This could lead to secret extraction from environment variables, instantiation of classes within trusted namespaces, and potentially arbitrary code execution via Jinja2 templates. Because LangChain is a foundational framework, every application built on it using the affected functions was vulnerable.
Key takeaway
Supply chain risk in AI is not limited to model weights and training data. The frameworks and libraries that developers use to build AI applications carry their own vulnerability surface. A single flaw in a foundational AI framework can propagate across thousands of downstream applications. Security teams need to track AI framework dependencies with the same rigor as any other software supply chain component.
8. Figma MCP RCE (CVE-2025-53967) - When Your Design Tool Executes Shell Commands
July/October 2025
Vector: Command Injection via Indirect Prompt Injection
What happened: A command injection vulnerability (in the Framelink Figma MCP server stemmed from a "design oversight" in its fallback mechanism. When the standard fetch API failed, the server fell back to executing curl commands via child_process.exec, directly interpolating URL and header values into shell command strings without sanitization. This allowed shell metacharacter injection (|, >, &&, etc.), leading to full remote code execution under the server process's privileges.
Since the Figma MCP server exposes tools to AI-powered coding agents like Cursor, an attacker could trigger the flaw through indirect prompt injection, tricking the MCP client into executing unintended commands. Exploitation could also be triggered by a remote attacker on the same network or through a DNS rebinding attack via a specially crafted website.
Key takeaway
MCP servers are rapidly becoming the connective tissue between AI agents and external tools. This attack showed that MCP server developers are making the same input sanitization mistakes that plagued web applications 15 years ago, but now with AI agents acting as unwitting intermediaries. Every MCP integration is a potential RCE vector until proven otherwise.
9. IDEsaster - 30+ CVEs Across Every Major AI Coding Tool
December 2025
Vector: Workspace Config Hijack via Prompt Injection
What happened: Researchers disclosed over 30 vulnerabilities spanning Cursor, GitHub Copilot, Windsurf, Roo Code, Zed.dev, and Claude Code. The attack pattern was consistent: prompt injection payloads hidden in code repositories could edit workspace configuration files and IDE settings to achieve remote code execution. The root cause was that auto-approval of in-workspace file writes was enabled by default across all tools. Every AI coding IDE that was probed turned out to be vulnerable.
Key takeaway
AI coding assistants operate with implicit trust in the workspace they're pointed at. That trust model is fundamentally broken. A poisoned repository becomes a weaponized environment the moment an AI assistant opens it. Organizations deploying AI coding tools need to enforce strict sandboxing, disable auto-approval for file writes, and treat every external code repository as untrusted input.
10. OpenClaw Prompt Injection - 21,000 Instances, Critical Infrastructure Exposed
March 2026
Vector: Prompt Injection + Data Exfiltration
What happened: Multiple AI-native vulnerabilities were discovered in OpenClaw, enabling prompt injection and data exfiltration at scale. Over 21,000 exposed instances were identified. CNCERT issued a warning that critical sectors, including finance and energy, faced potential leakage of core business data, trade secrets, and code repositories.
Key takeaway
hadow AI deployments at scale create national-security-grade exposure. When thousands of AI instances are publicly accessible without adequate security controls, the risk is no longer organizational. It is sectoral. Security leaders need continuous discovery mechanisms to identify every AI deployment across their environment, sanctioned or not.
What These 10 Attacks Tell Us
Three patterns cut across every attack on this list.
Prompt injection is the SQL injection of the AI era.
Seven of these 10 attacks involved some form of prompt injection, whether direct, indirect, or chained through agent-to-agent communication. EchoLeak, ForcedLeak, BodySnatcher, Gemini Trifecta, Figma MCP, IDEsaster, and OpenClaw all exploited the same fundamental weakness: AI systems that cannot distinguish trusted instructions from untrusted data. Defenses remain immature across every major platform. The vendors on this list are not startups. They are Microsoft, Salesforce, Google, OpenAI, and ServiceNow. If their AI products are vulnerable, yours likely are too.
AI agents expand the blast radius beyond anything traditional applications have created.
McKinsey's Lilli breach didn't just leak data. It exposed writable system prompts that could silently reprogram what 40,000 consultants were told. BodySnatcher didn't just bypass authentication. It turned ServiceNow's AI agents into an attacker's remote-controlled workforce. When an AI assistant can read your documents, invoke other agents, execute code, and access cloud infrastructure, a single vulnerability doesn't just create a data breach. It grants the attacker an autonomous operator inside your environment, one that moves faster than any human responder.
The AI supply chain is the next software supply chain crisis.
LangGrinch hit a foundational framework and propagated to every application built on it. Figma MCP showed that the connective tissue between AI agents and external tools carries the same input sanitization flaws web apps had 15 years ago. IDEsaster proved that the tools developers use to build software are themselves compromised. And OpenClaw demonstrated what happens when thousands of AI instances are deployed without anyone tracking where they are or whether they're secured. The stack your teams use to build, deploy, and connect AI is itself an attack surface.
What CISOs should prioritize in the next 6 months
The organizations hit hardest in these incidents shared common gaps. They trusted AI platform defaults. They treated prompts as configuration, not code. They focused guardrails on visible output channels and missed side-channel exfiltration. They had no inventory of where AI was deployed across the organization. And they relied on traditional scanners that couldn't keep pace with AI-speed adversaries.
Closing those gaps requires five shifts:
Treat system prompts as critical infrastructure. Implement version control, integrity monitoring, and strict write-access policies for prompts with the same rigor applied to production code deployments.
Adopt continuous AI red teaming. An autonomous AI agent breached McKinsey's platform in under two hours. Periodic penetration testing cannot match that velocity. Organizations need automated, continuous adversarial probing across prompt injection, authentication bypass, and data exfiltration vectors.
Maintain a complete inventory of AI deployments. OpenClaw exposed 21,000 unsecured instances. IDEsaster compromised every major AI coding tool tested. Shadow AI represents a material risk that cannot be mitigated without comprehensive discovery across the environment.
Harden the AI supply chain. Monitor framework dependencies for known CVEs, audit MCP server integrations for command injection vulnerabilities, enforce sandboxing for AI tooling, and disable permissive defaults such as auto-approval in coding assistants.
Extend monitoring beyond the prompt layer. DNS exfiltration, metadata encoding, and branch name injection all bypassed guardrails by operating beneath the application layer. Security controls limited to AI input and output channels leave the most sophisticated exfiltration paths undetected.
The question for CISOs is no longer whether your AI systems will be targeted. It is whether you will detect it when they are.
Experience enterprise-grade Agentic Security solution

