
Introducing Akto + Agentforce: Secure Your Salesforce Agent Fleet at Runtime
Learn how Akto and Agentforce protect Salesforce agents at runtime with real-time monitoring, security controls, and full visibility.

Krishanu
Salesforce is no longer just a CRM. It's becoming the platform where enterprises build, deploy, and run autonomous AI agents on top of their most sensitive data.
With Agentforce, teams can now build agents that qualify leads, draft customer responses, update opportunity records, run multi-step service workflows, and execute actions across the Salesforce ecosystem. All grounded in live CRM data.
Salesforce reports that Agentforce is now deployed across thousands of customer orgs, and the platform powers over 150,000 Salesforce customers worldwide. Every one of those agents has access to pipeline data, contact records, support tickets, and internal communications.
This is exactly the kind of rapid adoption that creates security blind spots.
Agentforce agents read external data through Web-to-Lead forms, retrieve internal CRM records, call external APIs, and execute actions autonomously. They inherit user permissions, read sensitive objects, and generate outputs that flow into downstream systems.
If something goes wrong, a poisoned lead form, a prompt injection, an over-permissioned agent, or an unintended data exposure, security teams need to know. And right now, most of them don't.
Today, we're introducing the Akto Salesforce Connector in Akto Argus, giving security teams complete runtime visibility into Agentforce agents running inside Salesforce.
Why Agentforce Needs Agentic Security
Agentforce agents are powerful.
They reason over CRM data, plan multi-step workflows, and execute actions across Salesforce objects without constant human guidance. They can read from any object the user has access to, write back to records, and call external services through approved actions and flows.
This capability introduces significant security and governance risk.
The ForcedLeak Problem
In September 2025, security researchers at fund ForcedLeak, a CVSS 9.4 vulnerability chain in Agentforce that allowed external attackers to exfiltrate sensitive CRM data through indirect prompt injection.
The attack worked through a deceptively simple chain. An attacker submitted a Web-to-Lead form with malicious instructions hidden in the description field. When an internal employee later queried Agentforce about that lead, the agent executed both the legitimate request and the attacker's hidden commands, exfiltrating CRM data to an attacker-controlled server through an expired whitelisted domain that cost five dollars to register.
Salesforce patched the trusted URL bypass on September 8, 2025, enforcing strict allowlists for Agentforce and Einstein AI.
But the structural problem with agents stayed.
The incident revealed something deeper than a misconfigured CSP. Agentforce agents read external data, hold private CRM context, and make outbound calls. That combination, what researcher Simon Willison calls the lethal trifecta, is present by design in nearly every Agentforce deployment. Patching one URL bypass does not remove it.
How Akto Secures Agentforce
Akto's Salesforce connector operates as part of Akto Argus. It connects directly to your Salesforce org through a Connected App and continuously monitors Agentforce activity.
1. Discover Every Agentforce Agent
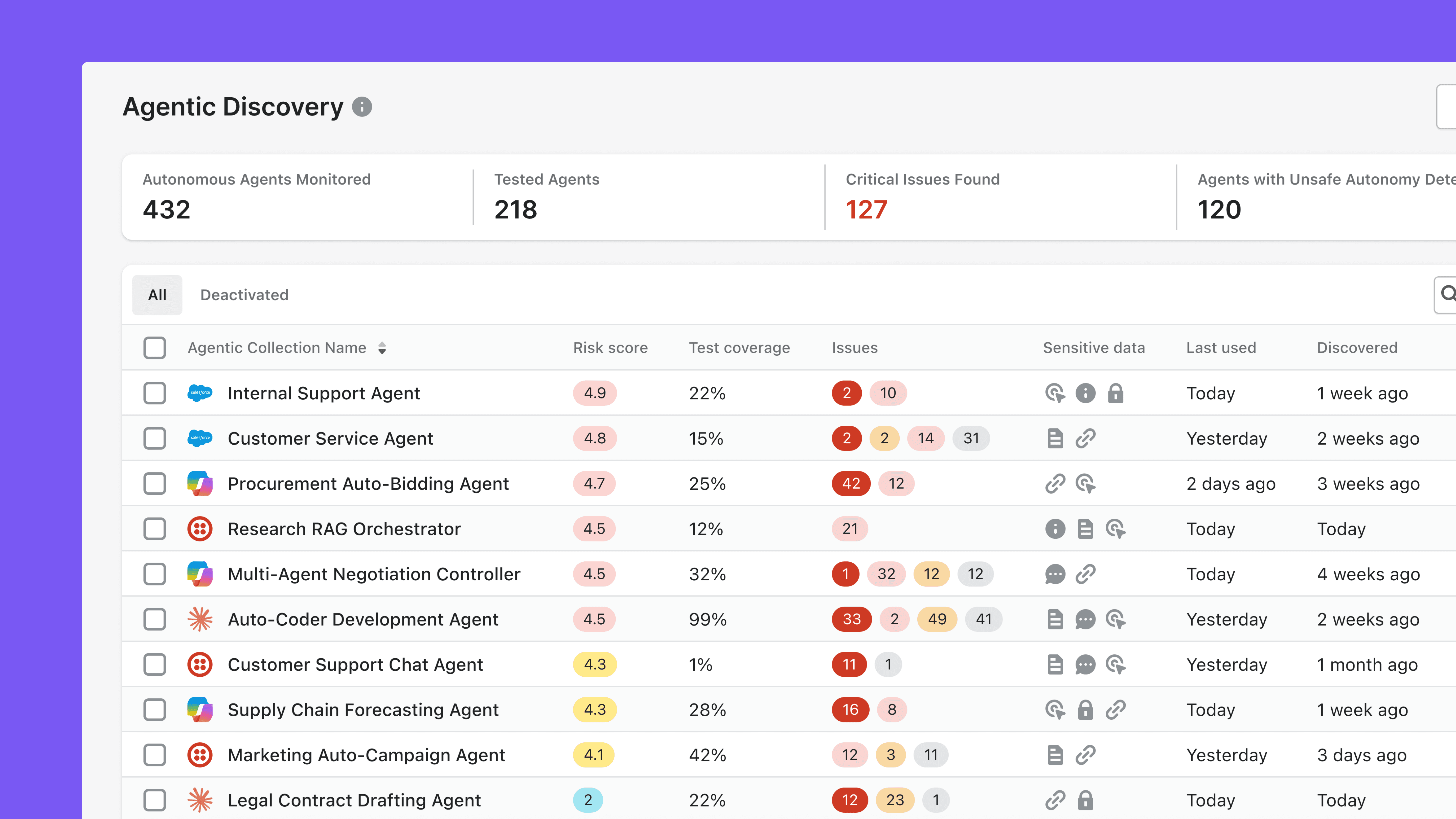
Once connected, Akto Argus automatically discovers all Agentforce agents and AI capabilities across your Salesforce org. This includes agents, topics, actions, prompt templates, and any custom agent implementations.
The result is a live, centralized inventory of every Agentforce agent in your environment, how it's configured, what model it's using, what topics it owns, and what data it can access.
For each agent, Akto identifies the sensitive data it can touch, PII, credentials, financial records, regulated data, so you know your blast radius before an incident, not after.
2. Observe Agent Configurations and Activity
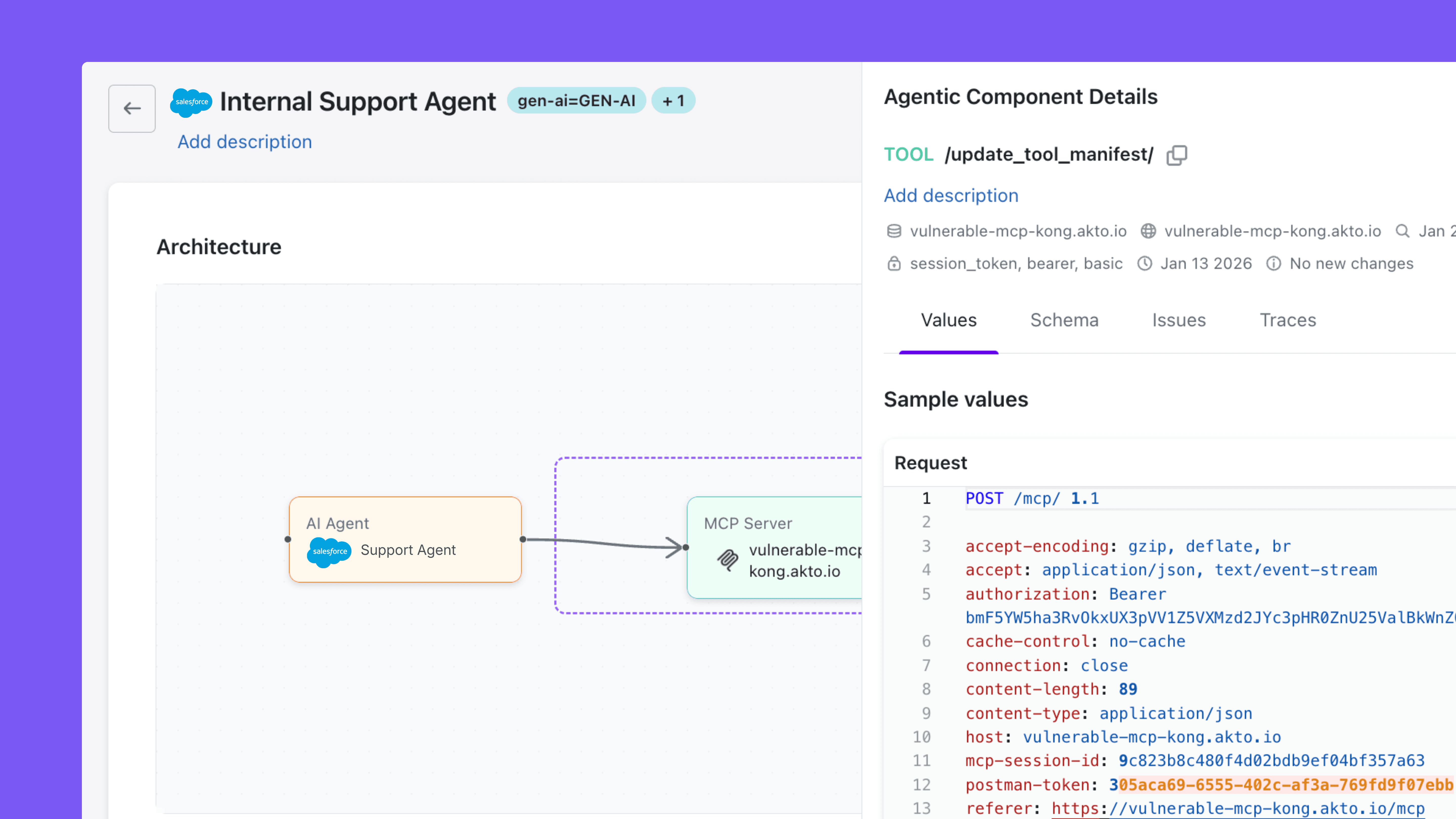
Akto captures Agentforce execution data continuously, giving security teams a rolling view of what agents are actually doing in production. This includes:
Agent configurations - all Agentforce agents and their configurations, including topics, actions, and prompt templates. This is your baseline for understanding what's deployed.
Agent execution metadata - models invoked, parameters set, and execution paths taken across every agent run.
Agent interactions and conversations - the prompts, queries, and inputs reaching agents from Web-to-Lead forms, internal users, and external channels. This is where you catch indirect prompt injection attempts and ForcedLeak-class payloads before they cause damage.
Input data - the full input data flowing into agent executions, including external data loaded into agent context. This is where you spot poisoned lead submissions and untrusted content reaching the agent's reasoning loop.
Output data - the responses agents generate and the outbound destinations they flow to. This is where you detect sensitive CRM data exposure, exfiltration attempts, and outputs that violate compliance requirements.
Action and MCP interactions - external tool and MCP calls executed by agents during a run. This is where you identify agents reaching out to systems they shouldn't be talking to.
3. Apply Guardrail Policies and Catch Violations Across Your Agent Fleet
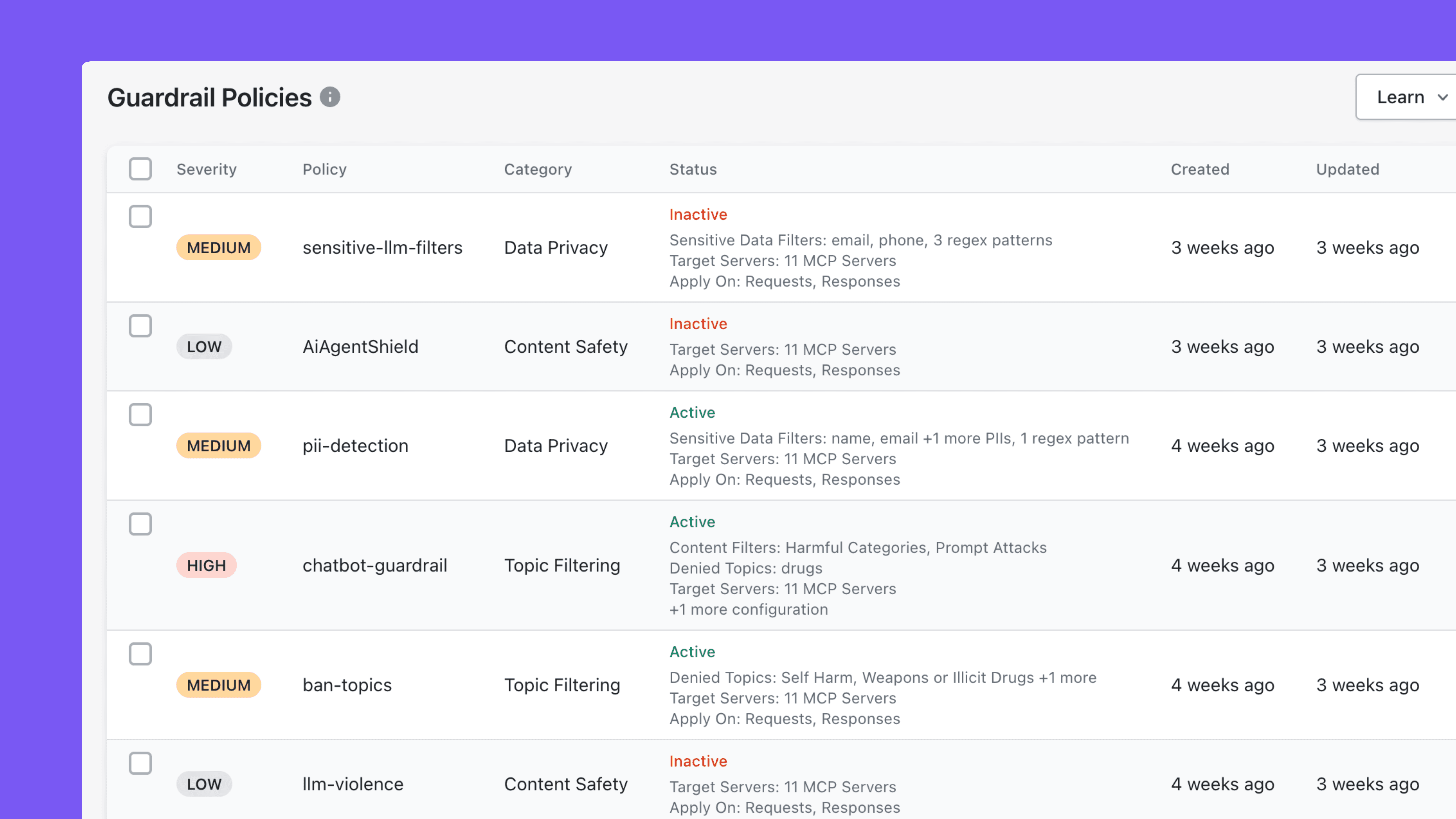
With discovery and monitoring in place, Akto Argus lets security teams apply guardrail policies across Agentforce activity.
Akto's guardrails run asynchronously alongside agent execution, logging every policy violation with full context. You can set up content and policy guardrails to flag what agents discuss or act on, prompt injection guardrails to detect ForcedLeak-class payloads embedded in Web-to-Lead forms and other external inputs, sensitive data guardrails to catch agents exposing PII, credentials, or regulated CRM data in their responses, untrusted URL guardrails to surface outputs sent to external destinations outside your trusted allowlist, language safety and abuse guardrails to flag harmful or off-policy outputs, and custom guardrails tailored to your organization's specific compliance and security requirements.
Every violation is logged with the full context security teams need: what was flagged, why, which agent triggered it, and what data was involved. From there, Akto Argus can be configured to block any flagged activity, giving security teams a clear path from detection to enforcement once policies are tuned.
This is how you build the audit trail and policy library that stops the next ForcedLeak before it spreads.
See your Agentforce security posture in one dashboard. Schedule a demo →
Getting Started: Five Minutes to Visibility
Setting up the Salesforce connector requires minimal effort. You'll need administrator access to your Salesforce org, an Agentforce license, and a running Akto Traffic Processor.
From there, the steps are straightforward:
Enable Agentforce in Salesforce under Setup → Feature Activation
Create a Connected App in Salesforce with OAuth enabled and the
apiscopeRetrieve the Consumer Key and Consumer Secret from the Connected App
Open Akto Argus → Connectors → AI Agent Security → Salesforce
Enter your Salesforce URL, Consumer Key, Consumer Secret, and ingestion endpoint
Click Connect and authorize the Akto Connected App in Salesforce
Akto immediately begins discovering Agentforce agents and collecting execution data. No changes to your Salesforce configuration.
Full setup instructions are available in our documentation.
Final Thoughts
The pattern is clear: every major SaaS platform has AI agents running inside it. Salesforce with Agentforce. ServiceNow with Now Assist. Microsoft with Copilot Studio.
Each platform creates its own agentic surface area, and each surface area introduces risks that traditional security tools weren't designed to handle. ForcedLeak proved it. The next ForcedLeak is already being researched somewhere right now.
That's what Akto Argus is built for: unified runtime security across every platform where your organization runs AI agents. The Salesforce connector is the latest addition to a growing list that already includes Snowflake, AWS Bedrock, Databricks, Azure AI Foundry, LangChain, Vertex AI, and more.
If your revenue and service teams are building with Agentforce, your security team needs visibility and runtime control over what those agents are doing. This is the fastest way to get it.
Ready to secure your Agentforce agents? Talk to us →
Experience enterprise-grade Agentic Security solution

