MCP Proxy: Security, Observability and Governance of Enterprise AI
Learn how MCP proxies enforce tool-level guardrails, block prompt injection and data exfiltration, and give security teams a full audit trail across every agent interaction.

Sucharitha
The Model Context Protocol (MCP) has become the backbone of modern agentic AI. It lets AI agents dynamically reach external tools, APIs, and live data sources in real time.
But as these systems grow more complex, the attack surface expands.
Secure, structured communication is no longer optional.
That’s when the MCP proxy acts as a middleware layer between AI agents and MCP servers. It enforces security policies and guardrails, translates protocols, and helps organizations implement threat protection at scale.
In this blog, we’ll decode everything the MCP proxy has to offer, along with use cases and best practices for implementation.
What Is MCP Proxy?
An MCP proxy is a bridge that sits between AI clients and MCP servers, managing every layer of their communication. It handles security enforcement, request routing, protocol translation, and logging, all from a single control point.
In simpler terms, it’s a controller for your AI infrastructure that prevents agents from connecting to external services and instead intercepts and governs each interaction before it goes through.
This creates a centralized control layer for all AI tool access, giving teams visibility and authority over what agents can reach. It acts as the critical gateway between AI agents and external services, ensuring no request slips through unchecked.
As a result, the MCP proxy keeps the whole system structured, scalable, and resilient.
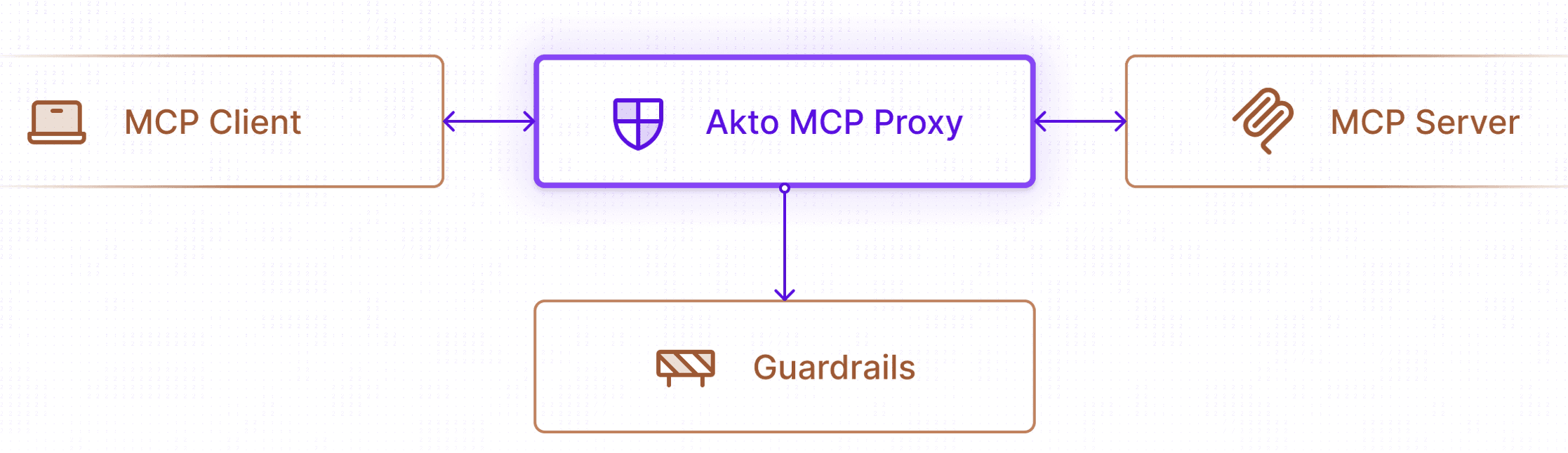
Akto MCP Proxy is a security and governance layer sitting between MCP clients and MCP servers
Why MCP Proxies Are Emerging
A few reasons why MCP proxies are the next big thing:
More and more businesses are implementing AI agents within their workflows. Therefore, a control layer is essential to manage them safely
Security threats and risks are growing day by day, and companies must avoid blind spots that could damage their reputation and customer trust
Governance is a must-have AI requirement. Teams must know what agents are doing and why
Coordination of multiple MCP servers without a central proxy leads to inconsistencies and poor visibility
Stakeholders now have strict requirements around access control, auditing, and compliance. MCP proxies make these possible at scale
How an MCP Proxy Works
An MCP proxy sits between your AI clients and MCP servers, acting as the single point of control for all agent communications. Every request must pass through it, and no one can bypass it.
Instead of allowing an AI system to directly interact with external tools, the MCP proxy routes and governs these interactions through a controlled layer.
The interaction follows a straightforward path like so:
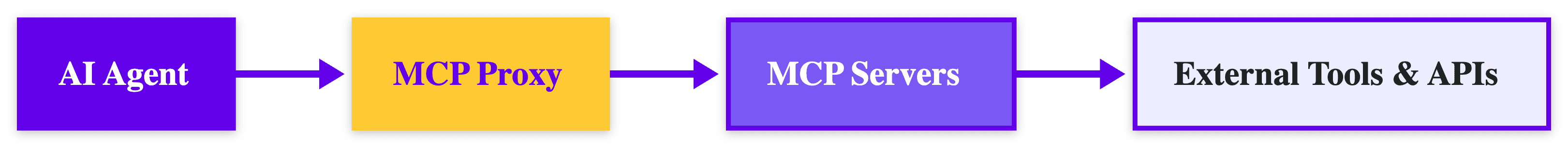
AI Agent → MCP Proxy → MCP Servers → External Tools and APIs
The proxy manages what moves through this path.
Along the way, it handles request routing to the appropriate server, enforces security policies before forwarding requests, adapts across transport protocols such as STDIO, HTTP, and SSE, and logs every tool interaction for full visibility and auditing.
Request Flow in an MCP Proxy
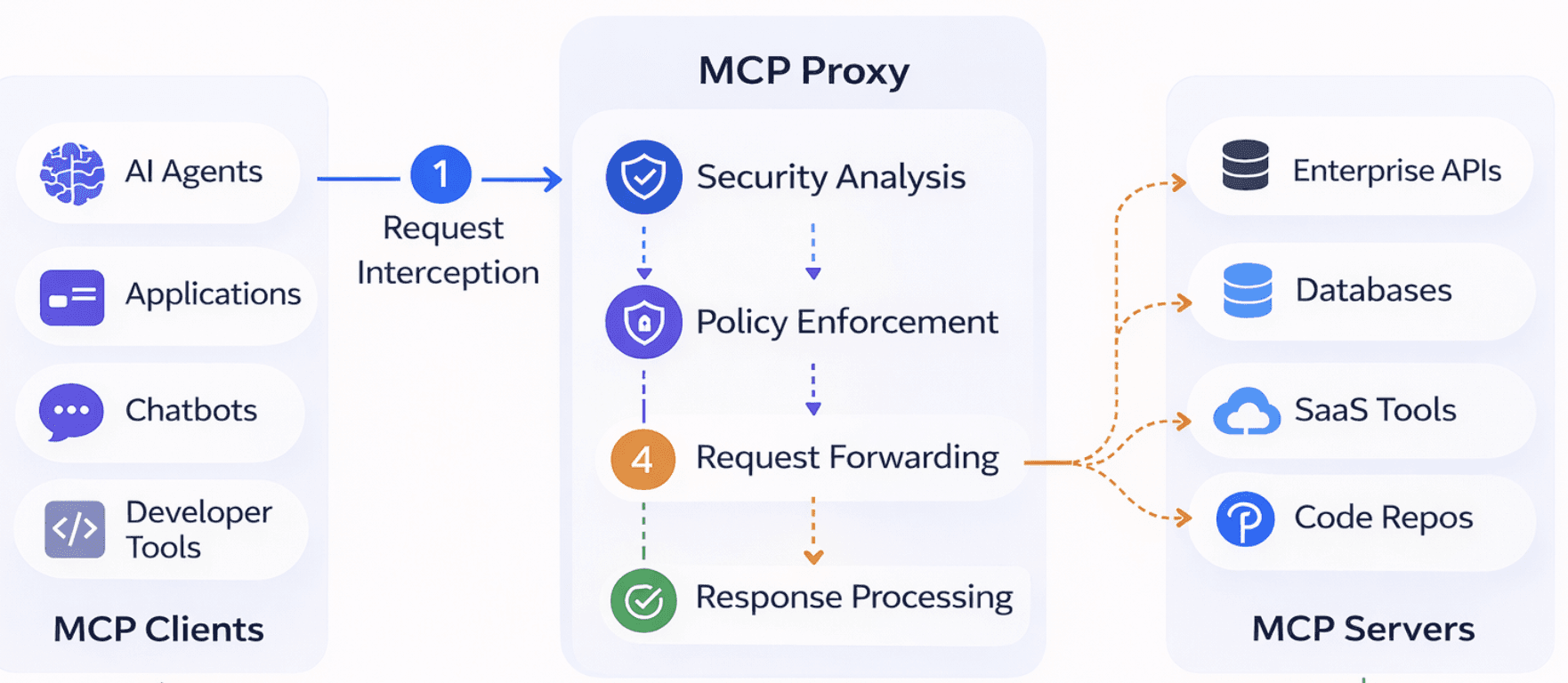
Here’s a real-time request flow of an Akto MCP Proxy in action:
Request Interception: MCP clients forward requests to the Akto proxy endpoint instead of directly to MCP servers
Security Analysis: Each request undergoes thorough threat detection and policy validation
Policy Enforcement: Requests are then evaluated against configured guardrails
Request Forwarding: Validated requests are forwarded to the original MCP server
Response Processing: Server responses are analyzed and returned to the client post-validation
Core Components of an MCP Proxy
Below are five primary components of an MCP proxy:
Request Router: Directs incoming agent requests to the correct MCP server based on set rules and internal architecture.
Security Policy Engine: Evaluates each request against configured guardrails. Blocks, flags, or allows based on its findings.
Authentication Layer: Verifies the identity of clients before any request moves forward. Supports API keys, tokens, and role-based access control.
Protocol Adapter: Translates between transport types such as STDIO, HTTP, and SSE, so agents and servers can communicate regardless of how they are configured.
Logging and Monitoring System: Captures a complete record of all requests, responses, threats detected, and guardrails applied, giving teams real-time visibility.
Why AI Agents Need an MCP Proxy
A lack of an efficient proxy lets AI agents connect directly to MCP servers, leading to unreliable security checks and zero insight into what agents are up to.
So, here are a few reasons why every AI agent needs an MCP proxy:
1. Managing Tool Access at Scale
Large organizations have dozens to even hundreds of tools across their AI infrastructure, making access management challenging to scale.
An MCP proxy helps centralize tool management into a single controlled point. Teams can define, update, and revoke access without interfering with individual server configurations.
2. Enforcing Guardrails for Tool Execution
MCP proxies let teams restrict tool usage based on agent identity, role, or context. They also prevent malicious prompts or commands from reaching servers.
Requests are scanned and evaluated before execution, allowing organizations to enforce strict guardrails that block unsafe tool calls, unauthorized data access, or prompt injection attempts.
3. Observability Across Agent Workflows
MCP proxies track every tool call, so teams have a full record of what was requested and when. Therefore, instead of second-guessing, teams can debug agents seamlessly by tracing request paths and reviewing audit logs to identify failure points.
4 Major Security Risks Without an MCP Proxy
Without a proxy layer as a bridge, common vulnerabilities go unchecked and unnoticed until damage is done. Here are four such major vulnerabilities:
1. Prompt Injection Leading to Tool Abuse
Prompt injection is one of the most powerful threats in agentic AI systems. A malicious input can manipulate an agent into calling unauthorized tools or returning unintended data.
Without a proxy enforcing execution policies, those calls go straight through the final endpoint, as the agent has zero security enforcements.
2. Unauthorized tool access
In-house agents must have controlled access to other internal tools, owing to the sensitive data enterprises hold. But without centralized access control, agents can end up reaching tools outside their scope.
3. Data Exfiltration Through Agent Tools
External APIs and tools are common channels for data leakage. An agent with unchecked access can pass sensitive information to an outside service.
Without a proxy scanning outbound requests, PII, credentials, and other ultra-confidential data can leave the organization undetected.
4. Lack of Visibility Into Agent Behavior
A lack of a proxy layer means there is no central monitoring or logging to track what agents are doing in real time.
And without audit logs, security teams cannot investigate incidents, and organizations cannot meet the governance requirements that regulators and stakeholders demand.
MCP Proxy Architecture for Secure AI Agents
A secure MCP proxy architecture places the proxy at the center of every agent interaction. This way, no request reaches an MCP server without passing through it first.
The structure follows a clear, layered path:
AI Agent
↓
MCP Proxy for AI agents (security + routing layer)
↓
Multiple MCP Servers
↓
External tools, APIs, and databases
Here’s a sample representation of a Cloud setup using Akto MCP Proxy:
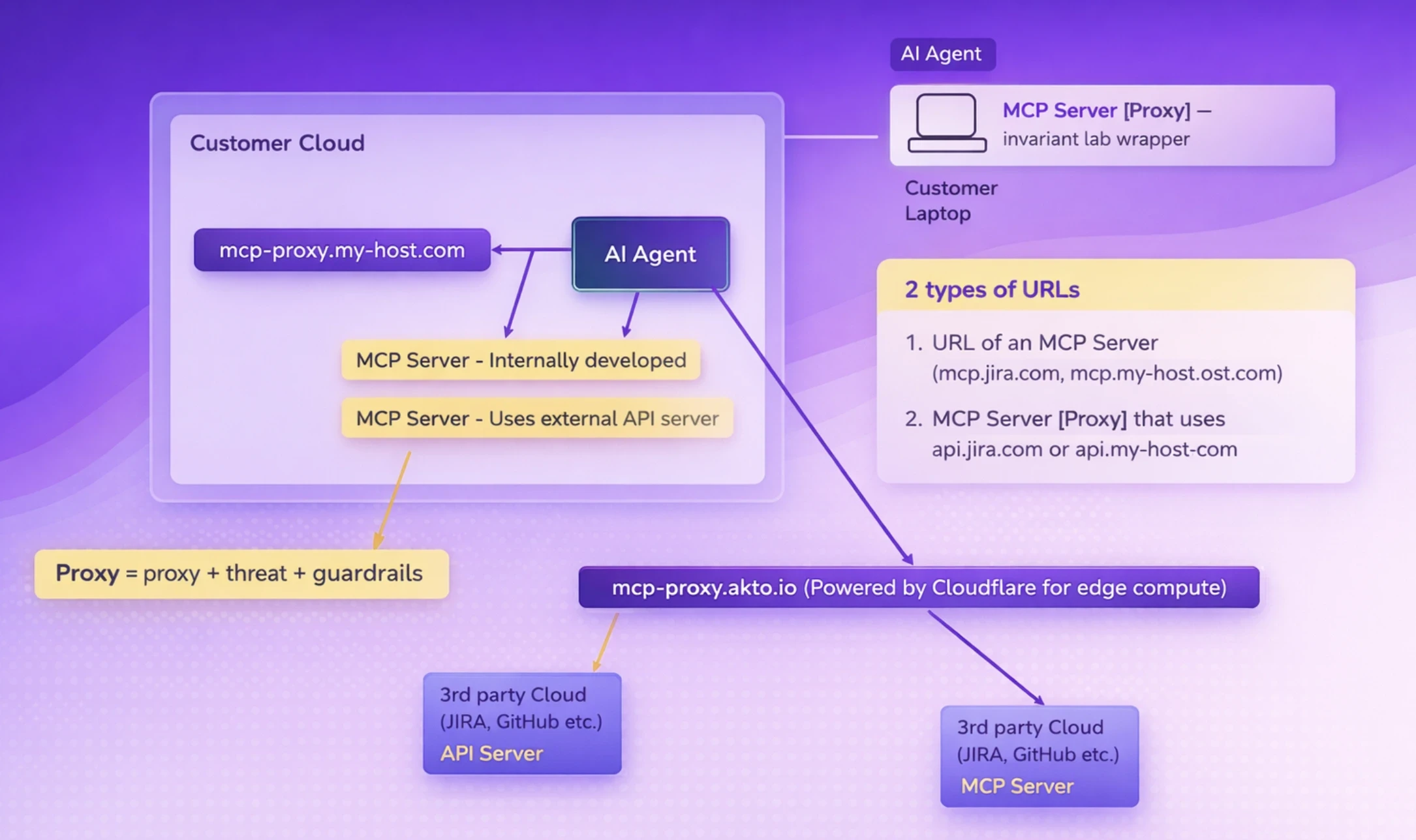
An MCP proxy is similar to an API gateway but tailored for AI agents. Similar to how an API gateway manages, secures, and monitors incoming traffic, an MCP proxy does the same for agent-to-tool interactions.
It validates requests, enforces policies, routes traffic to the right servers, and logs everything for seamless tracking.
Integrating MCP Proxy with LLM Applications
MCP proxies are designed to fit into existing AI stacks without requiring major restructuring. The proxy sits in front of your MCP servers, and your applications connect through it.
A typical integration pattern involves the following LLM applications:
AI chatbots: Route all tool calls through the proxy, ensuring every external interaction is validated and logged before execution.
Agent frameworks: Frameworks such as LangChain connect to MCP servers via the proxy endpoint. Guardrails are applied transparently in the background.
Enterprise AI assistants: These benefit from centralized access control, as different assistants can be granted different tool permissions from a single configuration layer.
Generative AI applications: Gen AI tools call external APIs or databases and pass those requests through the proxy, adding a security and observability layer without changing application logic.
The MCP proxy is also compatible with custom frameworks such as LangChain agents, LLM orchestration systems, and complex enterprise AI platforms.
Best Practices for Implementing an MCP Proxy
Getting an MCP proxy in place is only half the work. How you configure and maintain it determines how much protection it actually provides.
1. Restrict Tool Permissions
Every AI agent should only have access to the tools it genuinely needs. Applying least-privilege policies at the proxy level ensures that access is granted intentionally and not by default.
Define permissions by agent role or identity, and update them centrally without touching individual server configurations.
2. Monitor Tool Invocation Patterns
Normal agent behavior follows predictable patterns. However, during adversity, such as an agent calling unusual tools or a noticeable spike in request volume, is often the first signal of a problem.
Monitoring tool invocation patterns through the proxy helps catch abnormal behavior early. It also makes it easier to identify potential attacks before they wreak havoc.
3. Validate Inputs Before Tool Execution
Always keep an eye out for every prompt. Validating inputs at the proxy layer discards malicious content before it reaches the server or other tools.
Similarly, parameter validation adds another check by ensuring requests are as per the expected formats. These efforts help prevent prompt injection attempts.
4. Maintain Audit Logs for Agent Actions
Every tool call and agent request, input parameters, and outcomes must be recorded for a clear audit trail and logs.
When regulators or enterprise customers require proof of governance, a complete record of agent actions as compliance records is proof that security is in place.
4 Popular MCP Proxy Use Cases
Four use cases where MCP proxies are becoming a standard in AI deployments:
1. Enterprise AI Copilots
AI copilots are advanced virtual assistants that help increase an individual’s productivity and efficiency at work. For instance, few IT copilots can automate ticket resolutions, while HR copilots could help with onboarding.
A proxy ensures every interaction is authenticated, policy-compliant, and end-to-end logged. It also gives security teams complete visibility into communications.
2. Developer Assistants
AI developer assistants frequently call tools such as code executors, package managers, and deployment pipelines. A lack of efficient proxy and guardrails could cause a single bad prompt to trigger unintended actions in the production environment.
3. AI Automation Agents
Automation agents operate with minimal human interference, making governance even more critical. They often trigger dozens of tool calls across multiple systems simultaneously.
A proxy centralizes control and applies consistent policies, catches anomalous behavior in real time, and ensures automation workflows stay within intended boundaries.
4. Customer Support Bots
Customer support bots routinely handle PII, account data, and billing information. Any tool call that accesses such data needs to be strictly controlled and logged.
An MCP proxy adds a security layer between the bot and the tools so sensitive data is protected from mishaps, and every customer interaction has a full audit trail.
Future of MCP Proxies in AI Infrastructure
Some studies show that the global AI agents market is valued close to $8 billion and projected to reach $236 billion by 2036.
And only half of around 80% organizations have security policies in place to protect them. This gap pushes the need for MCP proxies, as governance becomes a must-have requirement.
Here’s what the future holds:
AI Security Gateways Are Becoming Standard
Investment in AI security is accelerating sharply. That’s because Shadow AI and unmonitored agent activity are driving some of the most expensive breaches and million-dollar losses organizations face today.
Agent Governance Platforms Are Gaining Urgency
Non-compliance can cost companies heavily. Regulators now urge that governance is a board-level priority.
MCP proxies provide the audit trails, access controls, and policy enforcement that governance platforms need to meet these obligations and satisfy AI compliance rules.
The Rise in Automated AI Risk Monitoring
Enterprises are actively switching to automated monitoring and reviews over manual security processes, making continuous risk monitoring a default standard. And MCP proxies are evolving alongside this shift.
Zero-Trust AI Architectures
Zero-trust is a security framework that applies the never trust, always verify principle to AI systems. Meaning, every access request, whether by a user, AI agent, or API, is verified in real-time and not just at the initial login. MCP proxies are the enforcement layer that makes zero-trust a reality in agentic systems.
Final Thoughts on MCP Proxy
As AI agents take on more complex tasks and connect to more external tools, securing that connectivity becomes the topmost priority.
MCP proxies provide the security, governance, and scalability that agentic AI systems need to operate safely in production environments.
Secure your MCP clients with Akto.
Akto MCP proxy gives organizations a transparent, policy-driven layer between AI agents and the tools they use, with real-time threat detection, guardrails, and complete visibility into every interaction.
With Akto, you can monitor AI tool interactions live, detect vulnerabilities in MCP-based architectures, and enforce security policies without slowing down your AI applications. Book a demo to see MCP security in action!
Important Links
Experience enterprise-grade Agentic Security solution

